Trezor Login – Secure Access to Your Hardware Wallet
Trezor Login is a secure authentication method that allows users to access their cryptocurrency wallets using a Trezor hardware device. Designed with advanced security in mind, Trezor Login eliminates the need for traditional passwords and replaces them with cryptographic verification. This ensures that only the physical device owner can access sensitive data, making it one of the safest ways to manage digital assets.
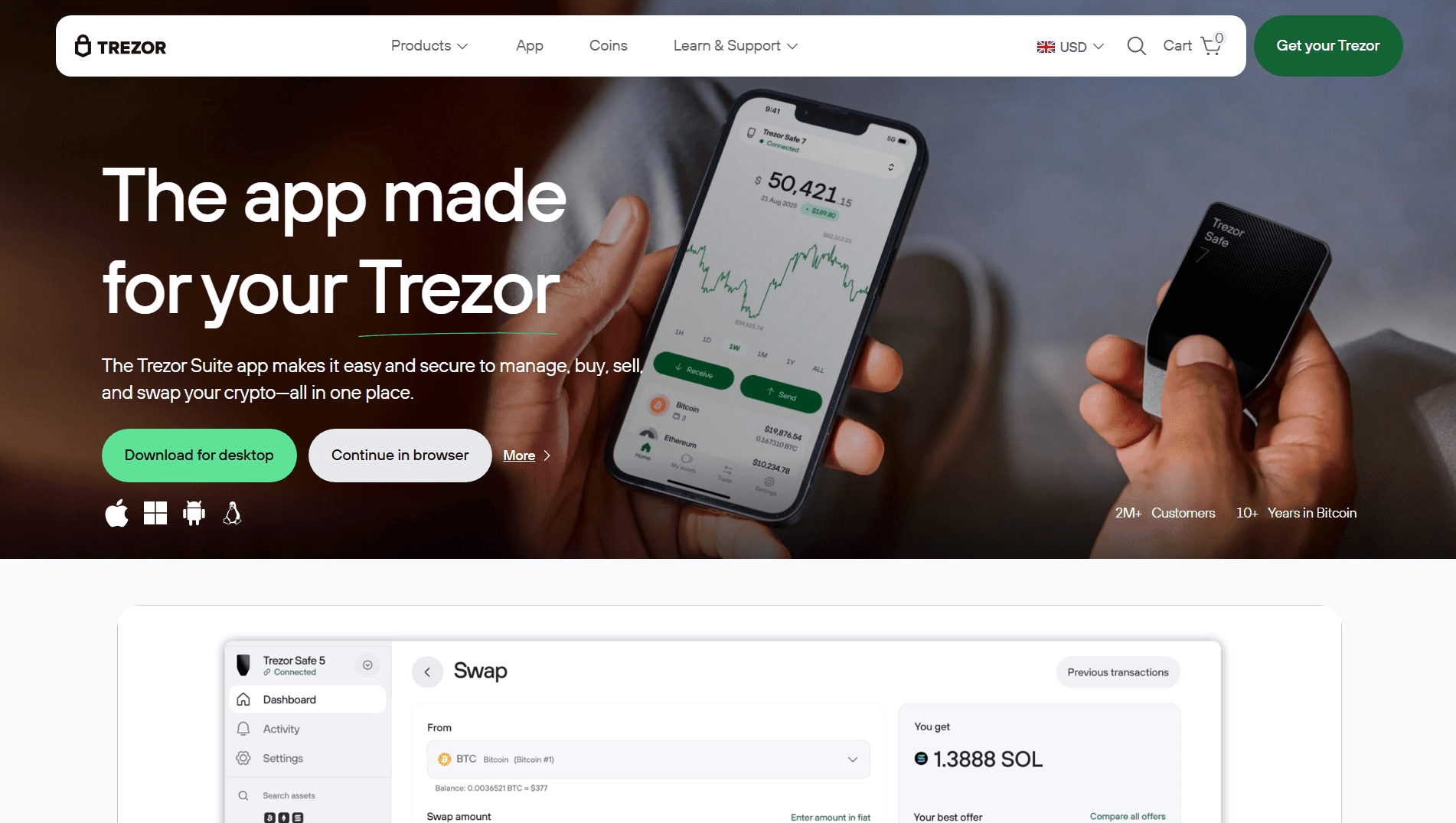
Trezor, developed by SatoshiLabs, is one of the leading hardware wallet providers in the cryptocurrency industry. With its offline storage capabilities and strong encryption, Trezor protects users from online threats such as hacking, phishing, and malware attacks. The login process is an essential part of this ecosystem, allowing users to securely connect to supported platforms and services.
What is Trezor Login?
Trezor Login is a passwordless authentication system that uses your Trezor device to verify your identity. Instead of entering usernames and passwords, users simply connect their hardware wallet and confirm the login request directly on the device.
This method is based on public-key cryptography, where the private key never leaves the Trezor device. As a result, even if your computer is compromised, your login credentials remain safe. Trezor Login can be used with supported websites, applications, and the official Trezor Suite platform.
How Trezor Login Works
The Trezor Login process is simple yet highly secure. Here’s how it works:
Connect Your Device
Plug your Trezor hardware wallet into your computer or mobile device.Open Trezor Suite or Supported Platform
Navigate to the platform where you want to log in.Initiate Login Request
Click on the “Login with Trezor” option.Verify on Device
A login request will appear on your Trezor screen. Confirm the request by pressing the physical button on your device.Access Granted
Once verified, you are securely logged in without entering any passwords.
This process ensures that only someone with physical access to the Trezor device can approve login attempts.
Key Features of Trezor Login
Trezor Login offers several powerful features that enhance both security and convenience:
Passwordless Authentication: No need to remember or store passwords
Two-Factor Security: Combines device possession with user confirmation
Phishing Protection: Prevents fake websites from stealing credentials
End-to-End Encryption: Keeps login data secure at all times
User Privacy: No personal data is shared during login
These features make Trezor Login an ideal solution for users who prioritize security in their digital activities.
Benefits of Using Trezor Login
One of the biggest advantages of Trezor Login is its ability to protect against common cyber threats. Traditional login systems rely heavily on passwords, which can be weak, reused, or stolen. Trezor eliminates this risk by using hardware-based authentication.
Additionally, the login process is quick and user-friendly. With just a few clicks and a confirmation on your device, you can access your accounts without typing anything. This not only improves security but also enhances the overall user experience.
Another benefit is compatibility. Trezor Login can be integrated with various services, including cryptocurrency platforms, password managers, and secure websites. This makes it a versatile tool for managing both financial and personal data.
Security Best Practices
While Trezor Login is inherently secure, users should follow best practices to maximize protection:
Keep Your Device Safe: Store your Trezor in a secure location
Backup Your Recovery Seed: Write it down and keep it offline
Verify URLs: Always ensure you are on the official website before logging in
Update Firmware Regularly: Keep your device up to date
Enable Passphrase Protection: Add an extra layer of security
By following these steps, users can significantly reduce the risk of unauthorized access.
Common Login Issues and Solutions
Although Trezor Login is designed to be seamless, users may occasionally encounter issues. Here are some common problems and their solutions:
Device Not Detected:
Ensure your USB connection is secure and install Trezor Bridge if needed.Browser Compatibility Issues:
Use supported browsers like Chrome or Firefox.Firmware Outdated:
Update your Trezor firmware through Trezor Suite.Login Not Confirmed:
Check your device screen and confirm the request manually.
Most issues can be resolved quickly by following these troubleshooting steps.
Trezor Login vs Traditional Login Methods
Compared to traditional login systems, Trezor Login offers superior security and convenience. Password-based systems are vulnerable to phishing, brute-force attacks, and data breaches. In contrast, Trezor uses cryptographic authentication that cannot be easily compromised.
Moreover, Trezor Login removes the burden of remembering multiple passwords. This reduces the likelihood of users resorting to weak or repeated passwords, which are common security risks.
Conclusion
Trezor Login represents a major advancement in digital security by combining hardware protection with user-friendly authentication. It provides a safe, efficient, and password-free way to access your cryptocurrency wallets and online accounts.
As cyber threats continue to evolve, adopting secure login methods like Trezor Login is more important than ever. By using a hardware wallet for authentication, users can take full control of their digital security and protect their assets from unauthorized access.
Whether you are a beginner or an experienced crypto user, Trezor Login offers a reliable and future-proof solution for secure account access.